Zimperium, a prominent cybersecurity firm, has identified 40 new variants of the TrickMo Android banking trojan. These variants have been linked to 16 droppers and 22 command-and-control (C2) infrastructures. As per the report, the latest version comes with enhanced features specifically designed to steal users’ Android PINs. TrickMo first gained popularity back in 2020. Now it has become sophisticated and poses a significant threat to Android users.
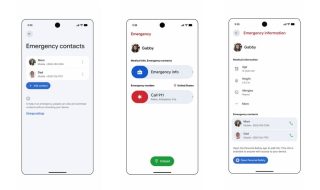
Zimperium’s researchers revealed that TrickMo now deploys a fake lock screen on Android devices and the screen looks like the legitimate Android unlock screen. When users enter their credentials, the malware transmits this sensitive information to an external PHP script hosted by the attackers. The stolen PINs allow attackers to unlock the victim’s device when it is not being monitored and perform fraudulent activities like unauthorized transactions.

The malware has the ability to exploit Android’s Accessibility Service. It can automatically grant itself additional privileges to perform more activities. It also serves phishing overlays to trick users into entering banking credentials and perform unauthorized financial transactions.
The report claims that the malware has already compromised at least 13,000 devices and victims primarily located in Canada followed by United Arab Emirates, Turkey, and Germany.
TrickMo is spread through phishing campaigns. Users generally receive malicious APK files via SMS or direct messages. To keep devices safe, users are advised to refrain from downloading apps from unknown sources. Always download apps from the Play Store. If you need to download APKs, always use trusted APK download websites.
TrickMo has also expanded its reach to various type of apps, such as VPNs, streaming platforms, e-commerce, trading apps, social media, and enterprise applications. This has been done to infect wide user base
Here are some tips to stay safe from TrickMo malware
- Avoid downloading APK files from unknown sources, especially via SMS or direct messages.
- Ensure Google Play Protect is enabled on your device.
- Regularly update your apps and OS updates to protect against vulnerabilities.
- Always notice any unexpected prompts for credentials on unfamiliar screens.
News Source: Bleeping Computer
Also see: