These days, no one would give the green light for a software release without taking care of security. It’s a critical part of development. Cyber attackers elaborate ways to steal sensitive data, and websites that don’t take measures to safeguard their systems put themselves at serious risks.
The flipside of the coin? While everyone is well aware of the importance of security, many find it hard to balance two things. On the one hand, security is paramount, but on the other hand, it’s essential to deploy fast. When the world is moving at a speed as crazy as this, any delay can set you miles back from the competition.
This is why it’s important to make sure that both SAST (Static Application Security Testing) and SCA (Software Composition Analysis) are tuned to work properly together so no security issue can slip. At the end of the day, developers are all people, and there’s always a chance of human oversight.
Let’s take a closer look at the differences between SAST vs SCA and how to balance them in DevSecOps to release robust software and applications.
What Are SAST and SCA?
Before we get into the details, let’s first answer the question of what SAST and SCA tools exactly are and what purposes they serve.
SAST is a tool designed to scan source code for vulnerabilities. It’s used in the early stages of the development process to identify issues like insecure coding patterns, logic flaws, and potential entry points for attackers.
SCA, on the other hand, is used to analyze dependencies. It goes over third-party libraries and open-source components to find known vulnerabilities, outdated versions, and license risks.
In layman’s terms:
- SAST = your code
- SCA = other people’s code you rely on
This is to answer the question about the key differences between SAST vs SCA. Both serve an important role in the development pipeline and can’t be overlooked.
Why You Need Both
Many teams make the mistake of leaning on just one tool. That’s where the problems come. You lock one door, but leave the other open, exposing your product to risks. Here’s why it’s essential to leverage both:
- SAST catches internal issues at the outset. It flags problems as developers write code, making it possible for them to fix bugs faster and cheaper.
- SCA protects your supply chain. Open-source components are all over the place today, and if one of them has a known vulnerability, your app inherits that risk.
- SAST and SCA cover different attack surfaces. One stays on guard of what you build, while the other one protects what you import.
If you skip one, you leave your software exposed to threats.
Advantages, Limitations, and When to Use Each
To get the most out of SAST and SCA, it helps to understand where their strengths lie and where they have limitations. Here’s a quick breakdown.
| Category | SAST (Static Application Security Testing) | SCA (Software Composition Analysis) |
| Advantages | Catches issues early while code is still being written, which makes fixes faster and cheaper. Gives clear, code-level insights so developers know exactly where the problem is. Also helps improve coding habits over time by flagging risky patterns. | Quickly detects known vulnerabilities in dependencies. Offers upgrade or patch suggestions, so teams don’t waste time figuring out fixes. Helps manage license risks and keeps your project compliant. |
| Limitations | Focuses only on your own code, so it won’t catch risks hiding in third-party libraries. Can produce noisy results, especially if not properly tuned. Also doesn’t cover runtime or environment-related issues. | Analyzes only dependencies, not your custom code. Relies on vulnerability databases, so new threats may go unnoticed. Large or complex dependency trees can make fixes harder to manage. |
| Use Cases | Best used during development and code reviews to catch vulnerabilities early. Works well inside IDEs and CI pipelines for continuous feedback. Ideal for enforcing secure coding practices across teams. | Best used when adding, updating, or auditing dependencies. Useful for tracking open-source risks, running license checks, and generating reports like SBOMs. Fits naturally into build and release stages. |
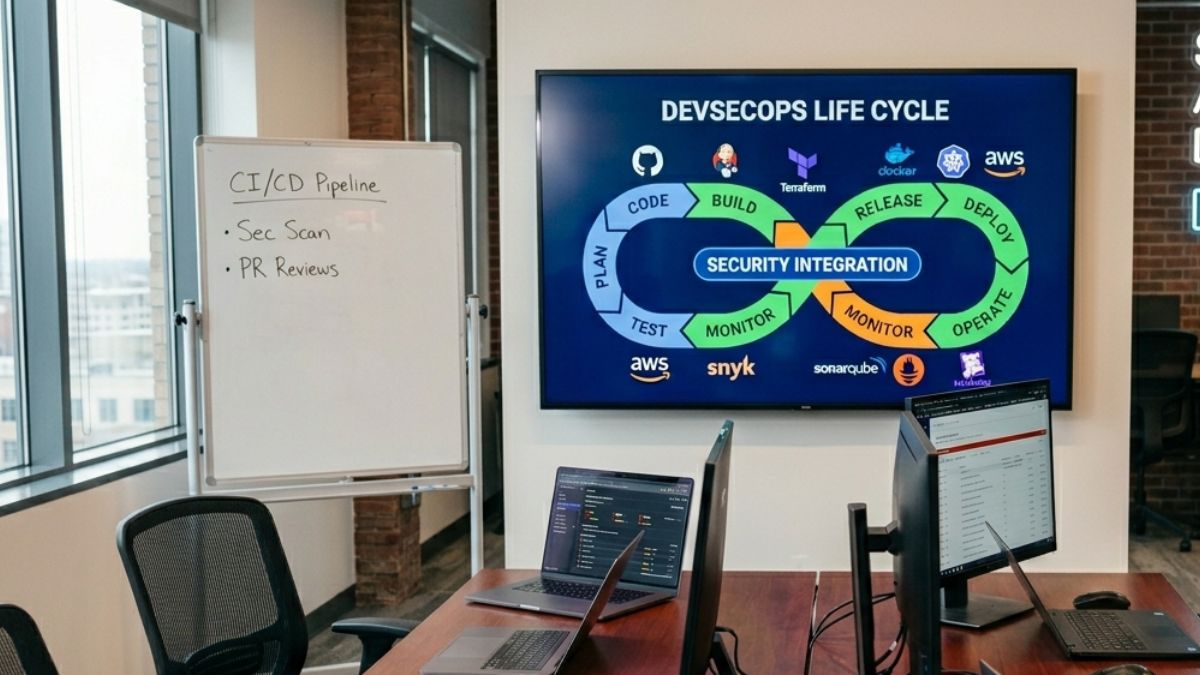
How to Balance SAST and SCA in DevSecOps
Now, we have finally come to the most interesting part – how to make these tools work together to deploy secure applications.
Start Early in the Pipeline
Shift security to the left. Run SAST as developers only write code or build stages. This way, if any issues were left unnoticed or not given enough attention, they will be immediately identified. SCA should be embedded into your pipeline early as well, so whenever a new dependency is added, it’s scanned for vulnerabilities and verified.
Set Clear Priorities
Not all vulnerabilities are created equal, and if you guard all of them, you will end up slowing down your workflow dramatically. To not compromise on speed, establish criteria for high and critical issues. These are the issues you should focus on first. Let low-risk issues go through notifications for now so as not to block releases. Keeping this balance is paramount.
Make Results Visible and Actionable
Use tools that support both SAST and SCA to solidify results in one place. This will simplify troubleshooting and reduce tool fragmentation, increasing the efficiency of developers’ work. Don’t just give a long list of notifications. Show them side-by-side and provide clear fix recommendations so teams know how to prioritize them correctly.
Monitor and Improve Over Time
Balancing SAST and SCA isn’t a one-and-done deal. It’s a living process that requires regular tweaks. Maintain up-to-date vulnerability databases, ensure the scanning rules are regularly updated, and keep tabs on the risks that emerge in dependencies and custom code.
Only by constantly monitoring the process and making timely adjustments will you be able to ensure your security setup stays effective over time.
Final Thoughts
Balancing SAST and SCA in DevSecOps isn’t about choosing one over the other. It’s about making them work in sync.
Think of it like a two-layer defense. SAST watches your code as it’s written, while SCA keeps an eye on the building blocks you bring in. When both run smoothly, you get better coverage without grinding development to a halt.
Get the balance right, and you will spend less time putting out fires, and more time building software that actually holds up under pressure.