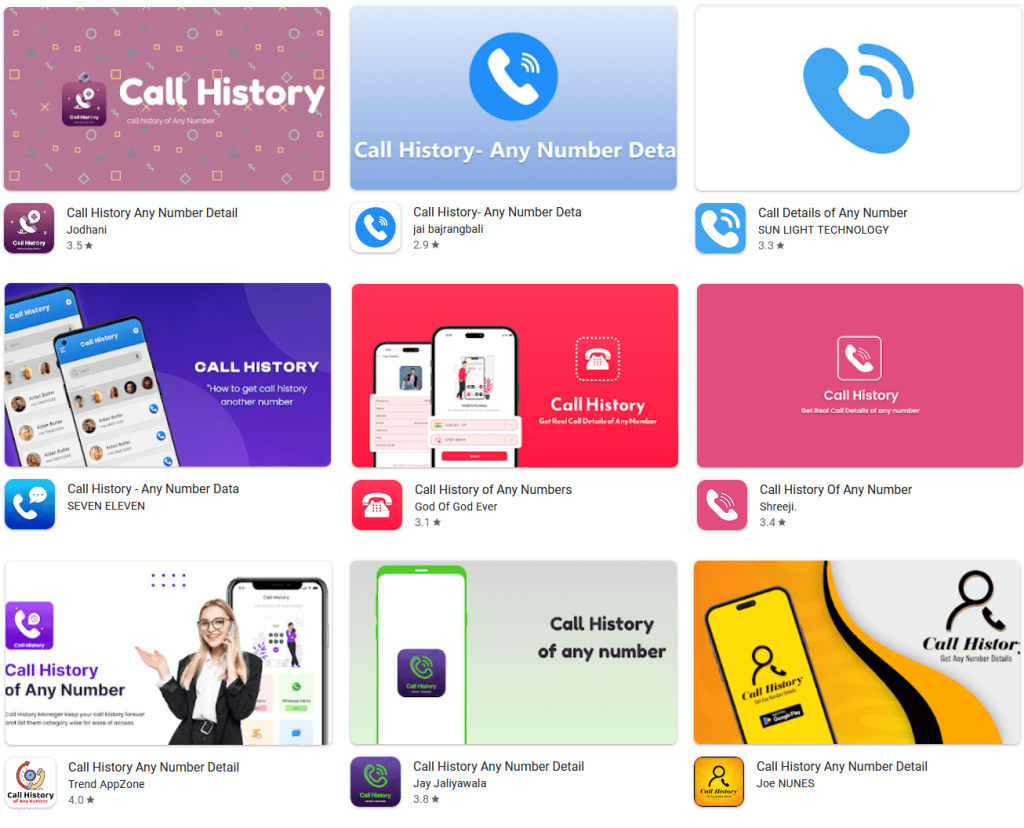
Researchers have uncovered a large-scale scam campaign involving 28 fake Android apps on the Google Play Store. These apps promised users the ability to check the call history of any phone number, but instead showed fabricated data and tricked users into making payments.
The malicious campaign, tracked as “CallPhantom,” was discovered by researchers at ESET WeLiveSecurity. According to the report, the apps were downloaded more than 7.3 million times before Google removed them from the Play Store in December 2025.
The apps mainly targeted users in India and other Asia-Pacific countries. Many of the apps came with India’s +91 country code pre-selected and supported UPI payments. This clearly shows that Indian users were a major target.
The scam worked by exploiting curiosity. The apps claimed they could reveal the call history of any mobile number. Users were shown partial call records that appeared genuine and were then asked to pay to unlock the complete details. However, the call history was completely fake.
Researchers found that all 28 apps used similar tactics despite having different designs and names. Some apps contained hardcoded names, timestamps, and fake call logs directly inside the app code. These fake records were mixed with randomly generated phone numbers to make the results appear believable.
Another set of apps asked users to enter their email address and claimed the complete call history would be delivered after payment. Even after users paid, no real data was ever provided.
Importantly, the apps never had the ability to access private call logs, SMS history, or WhatsApp chats from another person’s device.
This scam became successful because it abused both curiosity and lack of awareness. Many users still think apps can magically provide access to someone else’s private call records. In reality, no legitimate app can legally access another person’s call history or WhatsApp messages without direct permission and device-level access.
The apps also used multiple payment systems to avoid refunds. Some relied on Google Play billing, while others redirected users to third-party UPI apps or embedded card payment forms directly inside the app. Researchers say some payment details were fetched dynamically from Firebase databases. This allowed scammers to frequently change receiving accounts.
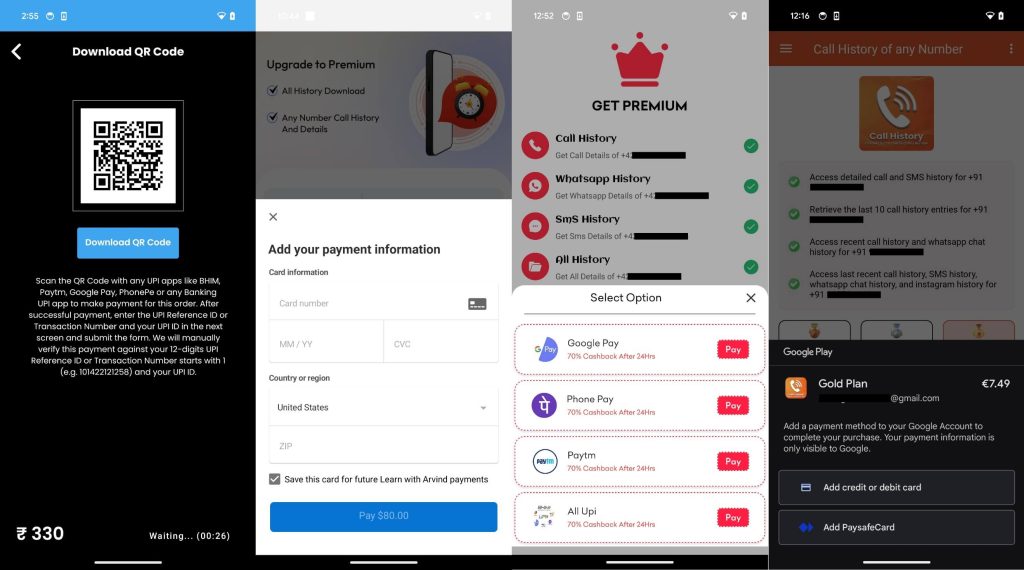
It is important to note how scammers tried to bypass Google’s refund protections. Payments made through external UPI apps or direct card forms could not be easily reversed through Google Play. This makes it harder for victims to recover their money.
Researchers also found deceptive notifications inside some apps. These notifications looked like legitimate email alerts and falsely claimed that call history results were ready. Tapping the notification redirected users to subscription payment pages.
The fraudulent apps charged users through weekly, monthly, and yearly plans, with some subscriptions costing as much as $80.
Also read: Microsoft Edge May Expose Saved Passwords in Memory, Company Calls It “By Design”
I strongly advise users to avoid apps that promise access to private information such as call logs, SMS records, WhatsApp chats, or social media activity of other people. These claims are almost always scams, spyware, or phishing attempts.
Users should also carefully check developer information before downloading apps. Recent reviews can also help users understand if the app is genuine. Stay cautious of apps asking for payments to unlock “secret” or “private” data.