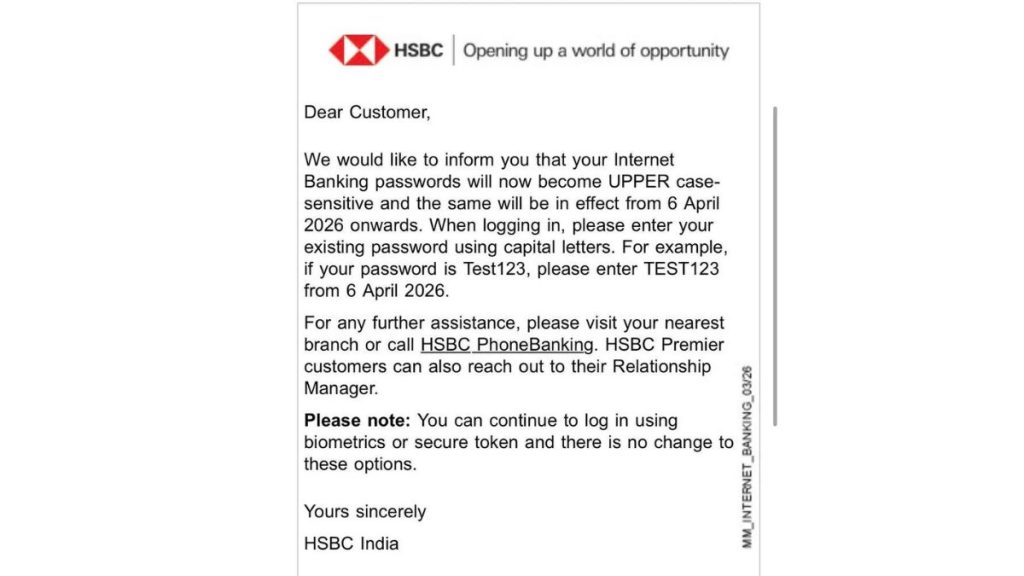
HSBC India has informed customers that their internet banking passwords will now become “uppercase-sensitive.” From April 6, 2026, users have to enter their existing password in all capital letters while logging in. For example, if your password was Test123, you now need to type TEST123.
At first, this looks like a small change. But technically, this should not happen in a properly designed system. And that is where the concern starts.
The bank is not asking users to reset their passwords. It is asking them to type the same password in uppercase. That means your existing password is still valid, but its uppercase version is now being accepted.
This directly points to how passwords are handled in the backend.
In a secure system, passwords are never stored in plain text. They are hashed. Hashing is a one-way process. Once a password is hashed, the original password cannot be retrieved, and the company cannot read it.
If the company cannot read your password, it should not be able to modify or reinterpret it later.
Even a small change in input, like converting Test123 to TEST123, should produce a completely different hash. Both should be treated as different passwords.
So how is this working?
One possibility is that the system was never truly case-sensitive. I checked HSBC’s website and found that passwords are not case sensitive. If that is correct, then Test123 and TEST123 were already treated the same.
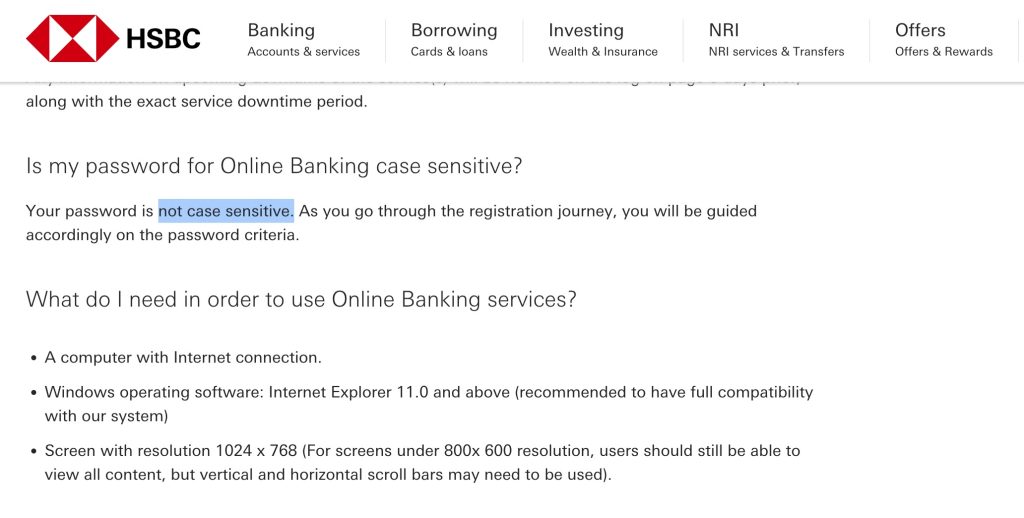
This suggests that the system was converting passwords to uppercase before hashing, and also converting user input to uppercase during login. In simple terms, passwords were always normalized.
Now it looks like the bank is removing that internal conversion and asking users to enter passwords in uppercase directly.
This is the only explanation that fits without assuming that the bank can read or modify stored passwords.
But even this is not ideal.
A secure system should treat different cases as different passwords. Forcing a single format reduces complexity and weakens password strength. It also shows that the system design is not following modern best practices.
If there was a need to change password handling, the correct approach was simple. Ask users to reset their passwords and enforce stronger rules going forward.
There is no good reason to change how existing passwords behave without a reset.
In the banking sector, security basics should not be compromised. Even a small change like this raises bigger questions about how systems are designed behind the scenes.











